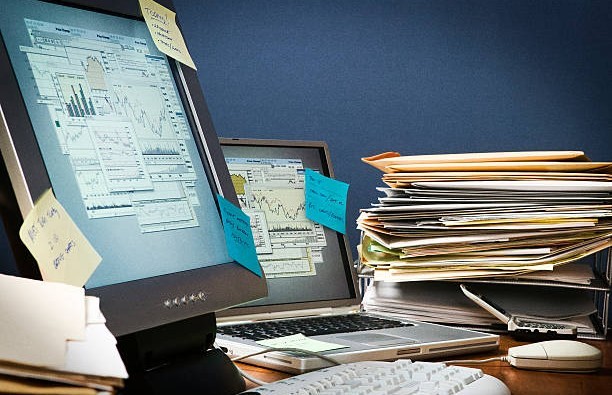
Software Sprawl: Why Too Many Tools Quietly Create Operational Risk
Software sprawl – the quiet buildup of too many overlapping, under-reviewed, or loosely managed tools – usually starts with a reasonable decision. A new platform solves a workflow problem. A team adopts a tool that helps it move faster. A department adds an application because the existing system feels too limited. Another subscription stays active … Read more